Kubernetes K8S在IPVS代理模式下Service服务的ClusterIP类型访问失败处理
时间:2020-09-10来源:www.pcxitongcheng.com作者:电脑系统城
背景现象
Kubernetes K8S使用IPVS代理模式,当Service的类型为ClusterIP时,出现访问service却不能访问后端pod的情况。
主机配置规划
| 服务器名称(hostname) | 系统版本 | 配置 | 内网IP | 外网IP(模拟) |
|---|---|---|---|---|
| k8s-master | CentOS7.7 | 2C/4G/20G | 172.16.1.110 | 10.0.0.110 |
| k8s-node01 | CentOS7.7 | 2C/4G/20G | 172.16.1.111 | 10.0.0.111 |
| k8s-node02 | CentOS7.7 | 2C/4G/20G | 172.16.1.112 | 10.0.0.112 |
场景复现
Deployment的yaml信息
yaml文件

1 [root@k8s-master service]# pwd 2 /root/k8s_practice/service 3 [root@k8s-master service]# cat myapp-deploy.yaml 4 apiVersion: apps/v1 5 kind: Deployment 6 metadata: 7 name: myapp-deploy 8 namespace: default 9 spec: 10 replicas: 3 11 selector: 12 matchLabels: 13 app: myapp 14 release: v1 15 template: 16 metadata: 17 labels: 18 app: myapp 19 release: v1 20 env: test 21 spec: 22 containers: 23 - name: myapp 24 image: registry.cn-beijing.aliyuncs.com/google_registry/myapp:v1 25 imagePullPolicy: IfNotPresent 26 ports: 27 - name: http 28 containerPort: 80

启动Deployment并查看状态

1 [root@k8s-master service]# kubectl apply -f myapp-deploy.yaml 2 deployment.apps/myapp-deploy created 3 [root@k8s-master service]# 4 [root@k8s-master service]# kubectl get deploy -o wide 5 NAME READY UP-TO-DATE AVAILABLE AGE CONTAINERS IMAGES SELECTOR 6 myapp-deploy 3/3 3 3 14s myapp registry.cn-beijing.aliyuncs.com/google_registry/myapp:v1 app=myapp,release=v1 7 [root@k8s-master service]# kubectl get rs -o wide 8 NAME DESIRED CURRENT READY AGE CONTAINERS IMAGES SELECTOR 9 myapp-deploy-5695bb5658 3 3 3 21s myapp registry.cn-beijing.aliyuncs.com/google_registry/myapp:v1 app=myapp,pod-template-hash=5695bb5658,release=v1 10 [root@k8s-master service]# 11 [root@k8s-master service]# kubectl get pod -o wide --show-labels 12 NAME READY STATUS RESTARTS AGE IP NODE NOMINATED NODE READINESS GATES LABELS 13 myapp-deploy-5695bb5658-7tgfx 1/1 Running 0 39s 10.244.2.111 k8s-node02 <none> <none> app=myapp,env=test,pod-template-hash=5695bb5658,release=v1 14 myapp-deploy-5695bb5658-95zxm 1/1 Running 0 39s 10.244.3.165 k8s-node01 <none> <none> app=myapp,env=test,pod-template-hash=5695bb5658,release=v1 15 myapp-deploy-5695bb5658-xtxbp 1/1 Running 0 39s 10.244.3.164 k8s-node01 <none> <none> app=myapp,env=test,pod-template-hash=5695bb5658,release=v1

curl访问

1 [root@k8s-master service]# curl 10.244.2.111/hostname.html 2 myapp-deploy-5695bb5658-7tgfx 3 [root@k8s-master service]# 4 [root@k8s-master service]# curl 10.244.3.165/hostname.html 5 myapp-deploy-5695bb5658-95zxm 6 [root@k8s-master service]# 7 [root@k8s-master service]# curl 10.244.3.164/hostname.html 8 myapp-deploy-5695bb5658-xtxbp

Service的ClusterIP类型信息
yaml文件

1 [root@k8s-master service]# pwd 2 /root/k8s_practice/service 3 [root@k8s-master service]# cat myapp-svc-ClusterIP.yaml 4 apiVersion: v1 5 kind: Service 6 metadata: 7 name: myapp-clusterip 8 namespace: default 9 spec: 10 type: ClusterIP # 可以不写,为默认类型 11 selector: 12 app: myapp 13 release: v1 14 ports: 15 - name: http 16 port: 8080 # 对外暴露端口 17 targetPort: 80 # 转发到后端端口

启动Service并查看状态

1 [root@k8s-master service]# kubectl apply -f myapp-svc-ClusterIP.yaml 2 service/myapp-clusterip created 3 [root@k8s-master service]# 4 [root@k8s-master service]# kubectl get svc -o wide 5 NAME TYPE CLUSTER-IP EXTERNAL-IP PORT(S) AGE SELECTOR 6 kubernetes ClusterIP 10.96.0.1 <none> 443/TCP 16d <none> 7 myapp-clusterip ClusterIP 10.102.246.104 <none> 8080/TCP 6s app=myapp,release=v1

查看ipvs信息

1 [root@k8s-master service]# ipvsadm -Ln 2 IP Virtual Server version 1.2.1 (size=4096) 3 Prot LocalAddress:Port Scheduler Flags 4 -> RemoteAddress:Port Forward Weight ActiveConn InActConn 5 ……………… 6 TCP 10.102.246.104:8080 rr 7 -> 10.244.2.111:80 Masq 1 0 0 8 -> 10.244.3.164:80 Masq 1 0 0 9 -> 10.244.3.165:80 Masq 1 0 0

由此可见,正常情况下:当我们访问Service时,访问链路是能够传递到后端的Pod并返回信息。
Curl访问结果
直接访问Pod,如下所示是能够正常访问的。

1 [root@k8s-master service]# curl 10.244.2.111/hostname.html 2 myapp-deploy-5695bb5658-7tgfx 3 [root@k8s-master service]# 4 [root@k8s-master service]# curl 10.244.3.165/hostname.html 5 myapp-deploy-5695bb5658-95zxm 6 [root@k8s-master service]# 7 [root@k8s-master service]# curl 10.244.3.164/hostname.html 8 myapp-deploy-5695bb5658-xtxbp

但通过Service访问结果异常,信息如下。
1 [root@k8s-master service]# curl 10.102.246.104:8080 2 curl: (7) Failed connect to 10.102.246.104:8080; Connection timed out
处理过程
抓包核实
使用如下命令进行抓包,并通过Wireshark工具进行分析。
tcpdump -i any -n -nn port 80 -w ./$(date +%Y%m%d%H%M%S).pcap
结果如下图:
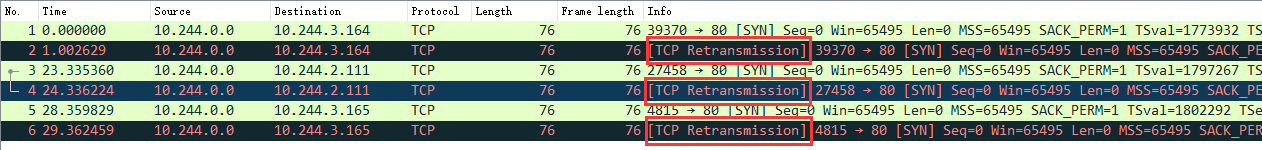
可见,已经向Pod发了请求,但是没有得到回复。结果TCP又重传了【TCP Retransmission】。
查看kube-proxy日志

1 [root@k8s-master service]# kubectl get pod -A | grep 'kube-proxy' 2 kube-system kube-proxy-6bfh7 1/1 Running 1 3h52m 3 kube-system kube-proxy-6vfkf 1/1 Running 1 3h52m 4 kube-system kube-proxy-bvl9n 1/1 Running 1 3h52m 5 [root@k8s-master service]# 6 [root@k8s-master service]# kubectl logs -n kube-system kube-proxy-6bfh7 7 W0601 13:01:13.170506 1 feature_gate.go:235] Setting GA feature gate SupportIPVSProxyMode=true. It will be removed in a future release. 8 I0601 13:01:13.338922 1 node.go:135] Successfully retrieved node IP: 172.16.1.112 9 I0601 13:01:13.338960 1 server_others.go:172] Using ipvs Proxier. ##### 可见使用的是ipvs模式 10 W0601 13:01:13.339400 1 proxier.go:420] IPVS scheduler not specified, use rr by default 11 I0601 13:01:13.339638 1 server.go:571] Version: v1.17.4 12 I0601 13:01:13.340126 1 conntrack.go:100] Set sysctl 'net/netfilter/nf_conntrack_max' to 131072 13 I0601 13:01:13.340159 1 conntrack.go:52] Setting nf_conntrack_max to 131072 14 I0601 13:01:13.340500 1 conntrack.go:83] Setting conntrack hashsize to 32768 15 I0601 13:01:13.346991 1 conntrack.go:100] Set sysctl 'net/netfilter/nf_conntrack_tcp_timeout_established' to 86400 16 I0601 13:01:13.347035 1 conntrack.go:100] Set sysctl 'net/netfilter/nf_conntrack_tcp_timeout_close_wait' to 3600 17 I0601 13:01:13.347703 1 config.go:313] Starting service config controller 18 I0601 13:01:13.347718 1 shared_informer.go:197] Waiting for caches to sync for service config 19 I0601 13:01:13.347736 1 config.go:131] Starting endpoints config controller 20 I0601 13:01:13.347743 1 shared_informer.go:197] Waiting for caches to sync for endpoints config 21 I0601 13:01:13.448223 1 shared_informer.go:204] Caches are synced for endpoints config 22 I0601 13:01:13.448236 1 shared_informer.go:204] Caches are synced for service config

可见kube-proxy日志无异常
网卡设置并修改
备注:在k8s-master节点操作的
之后进一步搜索表明,这可能是由于“Checksum offloading” 造成的。信息如下:

1 [root@k8s-master service]# ethtool -k flannel.1 | grep checksum 2 rx-checksumming: on 3 tx-checksumming: on ##### 当前为 on 4 tx-checksum-ipv4: off [fixed] 5 tx-checksum-ip-generic: on ##### 当前为 on 6 tx-checksum-ipv6: off [fixed] 7 tx-checksum-fcoe-crc: off [fixed] 8 tx-checksum-sctp: off [fixed]

flannel的网络设置将发送端的checksum打开了,而实际应该关闭,从而让物理网卡校验。操作如下:

1 # 临时关闭操作 2 [root@k8s-master service]# ethtool -K flannel.1 tx-checksum-ip-generic off 3 Actual changes: 4 tx-checksumming: off 5 tx-checksum-ip-generic: off 6 tcp-segmentation-offload: off 7 tx-tcp-segmentation: off [requested on] 8 tx-tcp-ecn-segmentation: off [requested on] 9 tx-tcp6-segmentation: off [requested on] 10 tx-tcp-mangleid-segmentation: off [requested on] 11 udp-fragmentation-offload: off [requested on] 12 [root@k8s-master service]# 13 # 再次查询结果 14 [root@k8s-master service]# ethtool -k flannel.1 | grep checksum 15 rx-checksumming: on 16 tx-checksumming: off ##### 当前为 off 17 tx-checksum-ipv4: off [fixed] 18 tx-checksum-ip-generic: off ##### 当前为 off 19 tx-checksum-ipv6: off [fixed] 20 tx-checksum-fcoe-crc: off [fixed] 21 tx-checksum-sctp: off [fixed]

当然上述操作只能临时生效。机器重启后flannel虚拟网卡还会开启Checksum校验。
之后我们再次curl尝试

1 [root@k8s-master ~]# curl 10.102.246.104:8080 2 Hello MyApp | Version: v1 | <a href="hostname.html">Pod Name</a> 3 [root@k8s-master ~]# 4 [root@k8s-master ~]# curl 10.102.246.104:8080/hostname.html 5 myapp-deploy-5695bb5658-7tgfx 6 [root@k8s-master ~]# 7 [root@k8s-master ~]# curl 10.102.246.104:8080/hostname.html 8 myapp-deploy-5695bb5658-95zxm 9 [root@k8s-master ~]# 10 [root@k8s-master ~]# curl 10.102.246.104:8080/hostname.html 11 myapp-deploy-5695bb5658-xtxbp 12 [root@k8s-master ~]# 13 [root@k8s-master ~]# curl 10.102.246.104:8080/hostname.html 14 myapp-deploy-5695bb5658-7tgfx

由上可见,能够正常访问了。
永久关闭flannel网卡发送校验
备注:所有机器都操作
使用以下代码创建服务

1 [root@k8s-node02 ~]# cat /etc/systemd/system/k8s-flannel-tx-checksum-off.service 2 [Unit] 3 Description=Turn off checksum offload on flannel.1 4 After=sys-devices-virtual-net-flannel.1.device 5 6 [Install] 7 WantedBy=sys-devices-virtual-net-flannel.1.device 8 9 [Service] 10 Type=oneshot 11 ExecStart=/sbin/ethtool -K flannel.1 tx-checksum-ip-generic off

开机自启动,并启动服务
1 systemctl enable k8s-flannel-tx-checksum-off 2 systemctl start k8s-flannel-tx-checksum-off
相关信息
-
-
2024-07-18
Centos 7 二进制安装配置 MariaDB数据库 -
2024-07-18
Centos7默认firewalld防火墙使用命令大全 -
2024-07-07
四种执行python系统命令的方法
-
-
linux 文件权限怎么解析
常用权限linux系统内有档案有三种身份 u:拥有者 g:群组 o:其他人这些身份对于文档常用的有下面权限:r:读权限,用户可以读取文档的内容,如用cat,more查看w:写权限,用户可以编辑文档x...
2024-07-07
-
如何使用WPSeku找出 WordPress 安全问题?
然而,如果我们遵循通常的 WordPress 最佳实践,这些安全问题可以避免。在本篇中,我们会向你展示如何使用 WPSeku,一个 Linux 中的 WordPress 漏洞扫描器,它可以被用来找出你安装...
2024-07-03
热门系统总排行
- 8726次 1 雨林木风Win10专业版64位纯净版系统官方下载
- 5396次 2 Win11官方最新版系统下载_Ghost Win11 22000.434(KB5009566)专业免激活版下载
- 4848次 3 电脑公司ghost win7 64位纯净专业版v2019.08
- 3285次 4 最新游戏专用Win11系统下载_游戏专用Ghost Win11 64位极速免激活专业版下载
- 2929次 5 深度技术 GHOST WIN10 X64 纯净版 V2019.09(64位)
- 2705次 6 Win10 21H1 esd镜像系统下载_Win10 21H1 64位免激活官方正式版下载V2021.04
- 2459次 7 深度技术 Ghost Win10 64位 免激活专业稳定版官网下载 V2021.12
- 2323次 8 电脑系统城ghost win7 sp132位 经典标准版 V2019.11
系统教程栏目
栏目热门教程
- 3675次 1 使用nginx代理gogs遇到推送代码错误的问题(RPC failed; HTTP 413 curl 22 The requested URL returned error: 413)
- 3393次 2 PVE连接Wi-Fi教程
- 3328次 3 supervisor重启服务失败
- 2779次 4 MobaXterm的基本使用与快捷键介绍
- 2526次 5 CentOS 8 系统图形化安装教程(超详细)
- 2232次 6 nginx报错[emerg] duplicate upstream
- 2168次 7 LINUX中如何查看某个端口是否被占用
- 2144次 8 spark报错:WARN util.Utils: Service 'SparkUI' could not bind on port 4040. Attempting port 40
- 2126次 9 CentOS7 多IP搭建SOCKS5代理服务器
- 2101次 10 Linux /etc/network/interfaces配置接口方法
人气教程排行
- 133852次 1 kimi智能助手网页版入口 kimi智能助手官网地址
- 94678次 2 win7旗舰版激活密钥大全
- 61046次 3 win10企业版激活密钥免费大全 win10企业版激活密钥2024最新
- 57442次 4 联想笔记本进入bios的三种方法 联想笔记本怎么进入bios
- 52523次 5 打印机为什么打印出来是黑的_打印出来纸张表面黑的解决方法
- 39952次 6 笔记本电脑序列号在哪|笔记本电脑序列号怎么看
- 34038次 7 对于目标文件系统文件过大无法复制到u盘怎么解决方法
- 33549次 8 kimi ai网页版地址分享 kimi ai官网地址入口
- 32916次 9 键盘全部按键没反应的解决方法 键盘被锁住按什么键恢复
- 31889次 10 键盘win键无效的解决办法 电脑win键失效怎么办?
站长推荐
- 14240次 1 Win11怎么激活?Win11系统永久激活方法汇总(附激活码)
- 12459次 2 如何用u盘装系统?用系统城U盘启动制作盘安装Win10系统教程
- 7178次 3 联想拯救者win10一键恢复如何使用_联想win10一键还原孔使用方法
- 6455次 4 怎么在u盘pe下给电脑系统安装ahci驱动
- 5994次 5 华硕笔记本bios utility ez mode设置图解以及切换成传统bios界面方法华硕笔记本bios utility ez mode设置图解以及切换成传统bios界面方法
- 5593次 6 联想电脑开机出现PXE-MOF:Exiting Intel PXE ROM怎么解决
- 3796次 7 win10怎么改为uefi启动_win10系统设置uefi启动模式的方法
- 2895次 8 MAC系统 win7/10/11电脑如何恢复到出厂系统 怎么把电脑恢复出厂设置
- 2526次 9 CentOS 8 系统图形化安装教程(超详细)
- 2435次 10 win10系统下检测不到独立显卡如何解决
热门系统下载
- 8726次 1 雨林木风Win10专业版64位纯净版系统官方下载
- 7163次 2 Windows Server 2019 官方原版系统64位系统下载
- 6282次 3 Windows Server 2008 R2 简体中文官方原版64位系统下载
- 6254次 4 Windows Server 2008 简体中文官方原版32位系统下载
- 5515次 5 网吧游戏专用Win7 Sp1 64位免激活旗舰版 V2021.05
- 5396次 6 Win11官方最新版系统下载_Ghost Win11 22000.434(KB5009566)专业免激活版下载
- 5325次 7 Windows Server 2012 R2 官方原版系统64位系统下载
- 4948次 8 系统之家最新GHOST WIN7 X64 纯净万能旗舰版系统下载
















